-
Crowd Funding for Independent Film (Series)
Last updated on July 6th, 2015 at 04:15 am I am writing a huge series of articles on crowd funding for independent productions. The emphasis is on international projects outside the USA. Taken together they form a comprehensive plan you can follow to launch your own crowd funding campaign. Crowd funding works even when it…
-
Good Review for Beijing Punk by The Impaler Speaks
Last updated on March 27th, 2017 at 02:18 pm Truly insightful analysis of the movie matched with deep knowledge of history & currency of punk. This guy gets it. “Beijing Punk” is fast-paced and fun, with a fantastic selection of music from the cream of the Chinese punk scene being heard the majority of the…
-
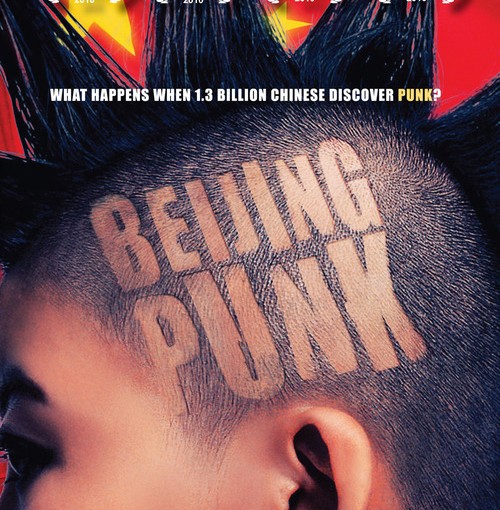
I Will Not Let An Exam Result Decide My Fate||Spoken Word
Last updated on July 6th, 2015 at 04:13 am I?m enjoying the spoken word piece I Will Not Let An Exam Result Decide My Fate by Suli Breaks. It?s a great track with an amazing video. Follow him on twitter at?https://twitter.com/sulibreaks I?m a father and have raised my kids (I hope) to value self reliance…
-
Don’t self host your website

Last updated on March 24th, 2017 at 02:27 am Should you use a free website from Tumblr or WordPress or Wix for the early days of ?your indie film? You should register on those free services to grab your brand name. But I wouldn?t go live with that for anything other than a teaser or…
-
French Hours

Last updated on March 27th, 2017 at 04:13 pm One of the films I’ve worked on did French Hours for one day of the shoot. Chances are unless you’re a film production geek you don’t know about it. Worse still you’ve come here to find out just what French Hours are all about. Hopefully you…
-
How to find unrated movies on any IMDB list
Last updated on July 6th, 2015 at 03:54 am I was trying to find which movies I hadn?t rated yet on my IMDB?list of movies I?ve?seen?- at least the movies I remember seeing there are lots of Westerns and SF movies whose titles I have no idea about. Anyway the trick is to add the…
-
7 Mistakes Filmmakers Make in Online Promotion – Video Extras

Last updated on March 24th, 2017 at 02:27 am All filmmakers want to get their shows seen, right? Uploading additional, extra and behind the scenes footage of your movie is a good opportunity to promote your project, aggregate an audience and create a moment of connection with fans and followers. However many filmmakers make these…
-
Short Sci-Fi Film: The Device

Last updated on July 6th, 2015 at 03:50 am The Device is a well executed, beautifully shot, science fiction short film with masterful special effects. I?ll be showcasing great SF and fantastical shorts as I find them. The quality of the lighting and camera work make this one special, Claude Lee Sadik and his team…
-
Address Book Related Names Completer Soon
Last updated on July 6th, 2015 at 02:41 pm I store all phone numbers and email addresses in the Address Book or Contacts app of the devices I use. On Apple Mac OS X it?s the Address Book app On IOS it?s the Contacts app On Android it?s Contacts On my webmail it?s Google?s Contacts…
-
Choosing a new laptop
Last updated on July 6th, 2015 at 02:41 pm My main workhorse is an eMachines eM250 10.1? netbook. All my email, calendar and important software works via the cloud so I can use any machine with a web-browser. I learned that lesson in the Great London Laptop Crash of 2008. However there are some items…